3 Cybersecurity Stories Businesses Need to Know About
I recently visited the set of Good Morning Connecticut to talk about the biggest cybersecurity stories in the news right now.
My goal was to cut through the ever-present din of data breaches and security tips to give viewers a broad overview and a key takeaway for each topic. In this post, I extend the analysis to the business perspective to see what lessons IT professionals and executives can glean.
Quest Diagnostics
In June, Quest Diagnostics, which has 20 locations in Connecticut, experienced a breach of 12 million patient records, including both financial and medical data. These are the two most valuable types of data on the black market and the most dangerous for identity theft, so this is a particularly potent breach.
The breach occurred through a "billing partner" of Quest called AMCA, which is actually a collections agency. Quest published an extensive FAQ about the breach, but the situation is pretty cut and dry: if you don’t have an overdue bill with Quest, you’re in the clear. This breach is sort of like the Equifax breach—a failure of a financial organization with which consumers did not make a conscious choice to do business. There's no way to "freeze" medical history like your credit, but it's a little known fact that you don't have to give your SSN to medical providers unless you are a Medicare or Medicaid recipient, so that’s one way to lower your risk of exposure to breaches of this type.
Third-party breaches are something we see fairly often at Kelser. When developing and implementing cybersecurity strategies for our clients, we always look at partner relationships to make sure that sensitive data is shared securely and not unnecessarily.
Key takeaway: The way your business shares information with partners needs to be part of your cybersecurity strategy.
Google Calendar
In a new kind of phishing scam, hackers place events in your Google Calendar which try to trick you into giving up information like a credit card number (some are disguised as contests, for instance).
The scam potentially affects the 1.5 billion users of Google Calendar. The fix is to change settings to show only invitations to which you've responded.
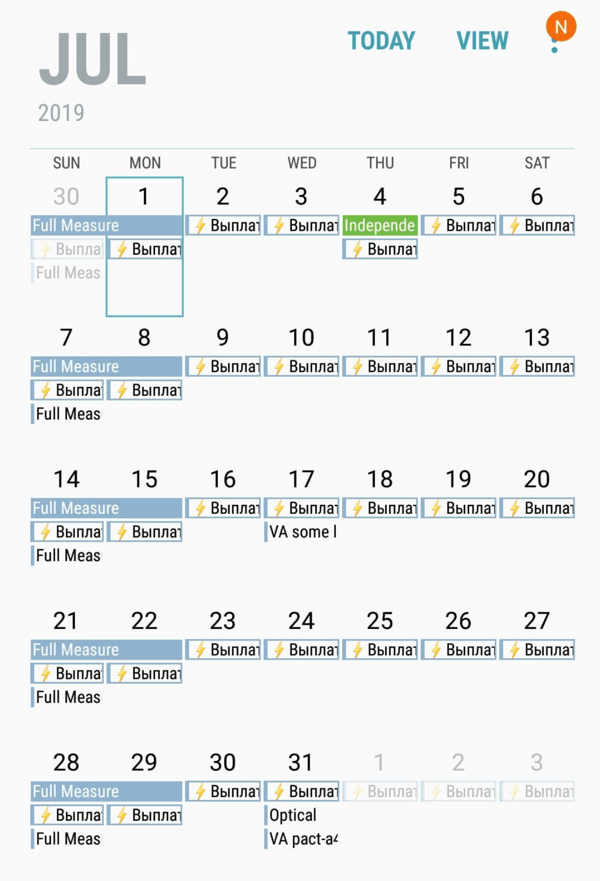
Kelser recently obtained a couple of exclusive screenshots of what this looks like. This user suddenly noticed events in Russian posted on every day of the calendar.
While this may seem like an extremely obvious sign something is wrong (and in this case the user shut down the phone immediately), the strategy here is for the hackers to catch you off guard. We’re used to seeing phishing emails, but a phishing calendar event might just be usual enough for users to forget to be careful. In fact, phishing often occurs via social media, text message, or even telephone.
Key takeaway: Phishing scams aren’t limited to email. Learning to recognize phishing wherever it occurs is essential to your company’s cybersecurity awareness training.
BlueKeep
In late May, a new vulnerability named “BlueKeep” was discovered in many versions of Windows that are out of support or nearing the end of support including:
- Windows 2000 (end of support)
- Windows 2003 (end of support)
- Windows Server 2003 (end of support)
- Windows XP (end of support)
- Windows Vista (end of support)
- Windows Server 2008 (scheduled end of support Jan 14, 2020)
- Windows Server 2008 R2 (scheduled end of support Jan 14, 2020)
- Windows 7 (scheduled end of support Jan 14, 2020)
These versions of Windows are used by about a third of the computers in the world. Windows 8 and 10 are not affected.
Hackers haven't yet developed a way to exploit the vulnerability on a large scale. However, the stakes are quite high because something very similar to this vulnerability is what enabled WannaCry in 2017, one of the largest cyber attacks ever that affected hospitals and major companies.
If you’re wondering how seriously to take this, note that Microsoft issued a fix for out of service versions of Windows. The only other time they have ever done so was WannaCry.
If users run a software update, manually download the patch from Microsoft, or update to a new version of Windows, they are protected from this vulnerability. Seems simple enough, right? For consumers, it generally is. Switching to a new version of Windows can be a big undertaking for a business, however, particularly if there is custom software on top of an old version.
For instance, a company may write their own code to automate a certain process on Microsoft Word. When new versions of Word are released, this automation no longer works, so the company decides to keep using an old version of Word. Eventually, this version is no longer supported and may end up being the reason the company can't update to a new version of Windows. Suddenly, the business is using an old, unpatched version of Windows—and leaving itself exposed—all in service to keeping its various tools working together. Cloud-based tools could avoid patch-related issues because they may not have to be updated on individual machines.
Key takeaway: Patching is important and it’s best to plan far in advance for updating to new versions of Windows.




