Common Threats to Mobile Security and How to Combat Them
 Securing today’s mobile workforce is becoming increasingly difficult. As the demand for remote productivity grows, so too does the sophistication of cyber-attacks aimed at road warriors. Some of today’s threats include mobile malware, eavesdropping, unauthorized access, and unlicensed or unmanaged applications. Let’s take a look at these threats and what can be done to combat them.
Securing today’s mobile workforce is becoming increasingly difficult. As the demand for remote productivity grows, so too does the sophistication of cyber-attacks aimed at road warriors. Some of today’s threats include mobile malware, eavesdropping, unauthorized access, and unlicensed or unmanaged applications. Let’s take a look at these threats and what can be done to combat them.
Common Threats to Mobile Security
- Mobile Malware and Android
- Unauthorized Access / Theft and Loss
- Unlicensed and Unmanaged Apps
- Eavesdropping
Mobile Malware and Android
Android continues to have the highest market share for mobile devices and is seeing a corresponding rise in exploits. From a security perspective, it’s a little scary because Android-based platforms allow applications from 3rd party app stores to be installed. Malware families such as ShiftyBug and GhostPush can easily root phones. Analysts have identified at least eight separate root exploits used in ShiftyBug alone. Today, these exploits are mainly delivering adware, but regardless, phones are being compromised and these rogue apps are nearly impossible to remove. Consider using a mobile anti-malware or anti-virus application such as those offered by McAfee (Intel Security) which can be found for free on Google Play. At Kelser, we also really like Cisco's AMP for Endpoints to combat against sophisticated modern threats.
Unauthorized Access / Theft and Loss
This attack often involves a hacker cracking passwords and gaining access to systems. Despite this persistent threat, many folks make the process even easier by having simple passwords like their home zip code, a relative’s birthday, or none at all. One way to enhance protection is to use hard passwords, with two words for example, and then to use biometrics like the fingerprint reader on devices like an iPhone(Touch ID) or Intel's True Key to unlock and automatically enter these more complex passwords for the user. Consider using multi-factor authentication (MFA) whenever possible and a solid mobile device management solution to detect, track, and remotely wipe devices should they fall into the wrong hands. Consider too using password managers that generate and store very strong and varied passwords. RoboForm is a good option.
Unlicensed and Unmanaged Apps
This can be a blind spot for admins, putting them at risk for audit and fines - never mind the damage that can be done by malicious apps. Consider mobile solutions that containerize and control enterprise applications.
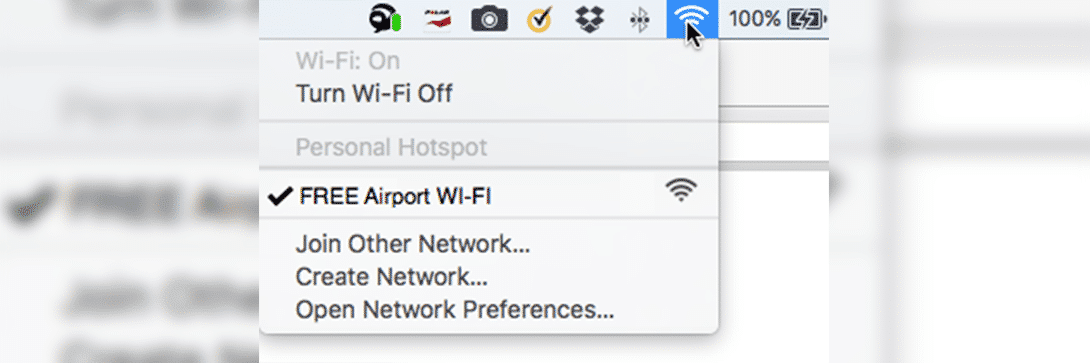
Eavesdropping
Free and public Wi-Fi is a great convenience but it’s also a potential trap for unsuspecting users. Hackers can set up their own wireless networks for the purposes of harvesting data. To protect mobile users, consider implementing mobile security software that can detect ARP spoofing and prevent connections. On your private networks, consider IPS and use settings like Dynamic ARP Inspection (see how on the Cisco 2960) that can also detect and stop these attacks. Also, consider multi-factor authentication (MFA), so even if a password is sniffed, the credentials can’t be used. Even Office 365 has MFA options. Another strategy is to leverage VPN, like Cisco AnyConnect, and micro-VPN technologies that route users through encrypted connections no matter their Wi-Fi connection.
Striking a Balance
In summary, organizations need to strike a balance between mitigating risk and empowering users by taking a defense-in-depth approach to protecting mobile users. IT teams need to have a blueprint for protecting the business that extends from endpoint to internet, and is tailored to the business’s needs. Want help creating your mobile security blueprint? Talk to Kelser about how, together, we can protect your mobile workforce and critical business data.
To learn more about improving your company's cybersecurity beyond mobile and other cybersecurity-related topics, check out this free eBook: