Cybersecurity Awareness Month 2020: Tips to Secure Your Business and Your Life
This isn’t news but cyber threats are a persistent issue for businesses and individuals alike in this day and age. If anything, the COVID-19 pandemic has worsened the threat landscape as cyber criminals are taking advantage of the related uncertainty and rapid transition to remote workforces and learning environments.
In Connecticut, we saw that firsthand as a ransomware attack locked down the first day for Hartford Public Schools last month. The City of Hartford’s response was exemplary as they did many things right before, during, and after the attack, but it served as a stark reminder of the ever-present threat of cyber criminals.
With October being Cybersecurity Awareness Month, I reached out to some cybersecurity and technology professionals for tips and insights to help you secure your businesses and home (as for many of us this year our home has become our office) in hopes of a more cybersecure tomorrow for everyone.
Be Vigilant and Verify Emails
With the constant onslaught of email, it is very important to pause for a moment when reading any email that asks you to do something. This becomes more important with the urgency of the request. Any email that asks you to do something immediately, whether it is an unusual or normal request, should be suspect.
Verify that the email is legitimate by calling, texting, or instant messaging the person making the urgent request; DO NOT reply to the email. Be vigilant and verify all email BEFORE you click on a link or open an attachment!
Watch Andrew’s tips in this video: https://share.vidyard.com/watch/1Vo1u7vNDc78aRLVTLNgpN?
It is also useful to check where the email came from by looking at the headers. In Outlook, with the email open and the active window, click “File” from the menu and then the “Properties” box. There is a box at the bottom called “Internet Headers.” Consider this the packaging that the urgent request came in.
A few simple things to check:
| Received-SPF: PASS | (a form of validation for the sender - SoftFail usually means bulk email) |
| Sender: <email address> | (should be who you think it is from) |
| FROM: <email address> | (should be who you think it is from and should match the sender) |
| Reply-To: <email address> | (should be who you think it is from) |
It only takes a moment to verify the email or to get an infection on your computer. Email is still the most prevalent attack vector. Be vigilant!
 - Andrew Tyler, Senior Consulting Engineer
- Andrew Tyler, Senior Consulting Engineer
Updated, Encrypted, and Secured
Keeping your devices patched and current is a must when it comes to the security of the device. Your work devices may be centrally monitored and managed with updates pushed out to them. For personal devices like PCs that are running Windows you can “Check for Updates” in system settings. There should generally be none outstanding.
Encryption can also go a long way towards protecting your data even if it falls into the wrong hands.
In Excel and Word, make use of “Encrypt with Password” on any documents containing remotely sensitive data. You can find it under File > Info > Protect Document. In current versions of Word and Excel this robustly encrypts the contents of the document.
If available, encrypt any email that contains sensitive information. Check with your email administrator or provider on how to do this.
Watch Jon’s tips in this video: https://share.vidyard.com/watch/bHRC4ZZHNN8T68hXytH5NZ?
The increase in remote workforces and employees relying on their home networks makes securing your home Wi-Fi more important than any time before. Use guest Wi-Fi access for visitors to keep them off the Wi-Fi network/SSID that has your PCs on it.
If you have IoT devices (security cameras, thermostats, security systems, video and music streamers) segregate the network they are on from where you connect your desktop or laptop.
Finally, if you receive text messages as part of MFA (multi factor authentication), make sure that your phone does not show contents of text messages on the home screen when it is locked.
Same goes for using an MFA application – it should not show any MFA codes on the locked home screen. If MFA codes are displayed on the lock screen and someone steals your device, then it is that much easier for them to access your most confidential accounts.
 - Jonathan Stone, Chief Technology Officer
- Jonathan Stone, Chief Technology Officer
Five Ways to Validate a Phishing Email
If you receive an email from someone you don’t know or an email from someone you do but they are asking you something out of the ordinary, consider these five things below when determining if it is a phishing email.
- Ask Why: If anyone asks about your personal information over email, don’t hesitate to ask WHY. A legitimate email will never ask personal information like your passwords or other personally identifiable information (PII).
- Think Before Opening: Always think twice before clicking any attachment or link in an email. Make sure it’s legit and came from someone you know or that you were expecting that email. That file or link could lead to something malicious.
- Verify Sender and Time: You should always verify a sender email address before replying. When dealing with work matters, a legitimate email should come from an organization’s email domain not from a personal email address. Work emails also typically come in during office hours - important emails frequently don’t come in after hours.
- Don’t Act Out of Pressure: If an email comes in asking you to do something urgently or ASAP, don’t immediately reply due to that pressure. Reach out to the email sender or appropriate department by phone or in person for validation.
- Report Phishing: Report the email if it seems like a phishing attempt. How that is done will vary by application, organization, and other factors so make sure to check with your appropriate department so you’ll know how to report one if it makes it into your inbox.
 - Suggatul Alam, Network Engineer
- Suggatul Alam, Network Engineer
Use Caution with Public Wi-Fi
Always use public Wi-Fi with caution. Even if a Wi-Fi network requires a password that you must obtain, it doesn’t mean the network is secure. Potential attackers can leverage that public Wi-Fi in order to compromise your sensitive personal and professional information.
If you must use public Wi-Fi, utilize a VPN solution in order to encrypt your traffic. The VPN solution adds another layer of protection and instills peace of mind.
 - Mark Lepak, Senior Network Engineer
- Mark Lepak, Senior Network Engineer
Think Before You Install
Always take caution with browser extensions. Though they may have the functionality you’re seeking, make sure to review their permissions, reviews, and the reputation of the developers.
It’s 2020, we all have mobile apps. If you no longer use the app, take the time to remove your account from the mobile app. Permissions and the security of apps can constantly change between updates as features are added and vulnerabilities uncovered. If you’re not keeping up with that app, even more reason to jettison it.
It’s also important to teach your children about good online habits. Explain the risks of technology and how to be responsible online. Reduce their risk by setting guidelines for and monitoring their use of the internet and other electronic media.
 - Tushar Dadarwala, Systems Engineer
- Tushar Dadarwala, Systems Engineer
If It’s Connected…
If It’s Connected, It Must Be Protected: Always make sure your devices have anti-virus/anti-malware protection, are up to date, and consider adding other layers of security where possible.
Look for the Lock: When browsing the internet, look for the lock symbol next to the web address which indicates that the site is secure.
![]()
If there isn’t a lock icon or if your browser presents a warning, think twice before you enter any personal or sensitive information on that web site. If you’re unsure if a site like that is safe to use, consult your IT or appropriate department.
 - Tom Carusone, Project Manager
- Tom Carusone, Project Manager
The Necessity for Complexity in Passwords
How secure is your password and how secure should it be?
If your password is changed every 90 days, you need a password that, on average, takes at least 91 days to crack. But how can you know how long your password would take to crack?
The following chart (from CloudNine) depicts how long it takes to crack a password of a given length and complexity. This one and others have been circling the internet for a long time.
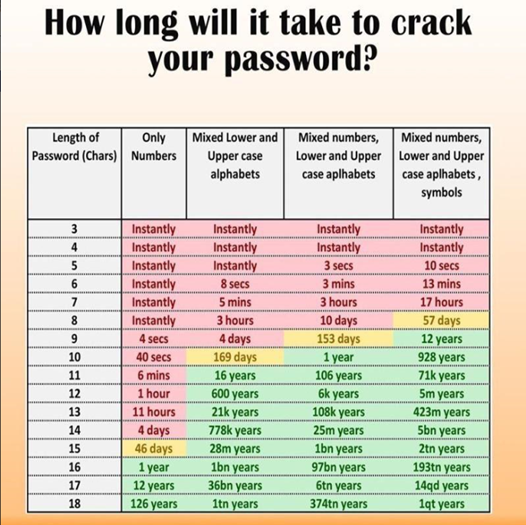
While it provides a useful guideline, it makes many assumptions. For example, the time period shown is for an “average” password of the complexity and length listed. It’s also basing these figures purely on brute force cracking with no other guidance.
To put that in context, it shows that a 12-character, numbers only password would take one hour to crack.
Who thinks “000000000001” will take the same amount of time as “654788139021”?
Most attempts are likely to sequence the possible passwords in some manner so passwords at either end of the sequence may not take close to the average time to crack.
Hackers make use of dictionary lists which present multitudes of common words and phrases then combine them with rule sets that define common substitutions to generate many potential alternatives per wordlist entry. For rule sets, think of things like replacing “a” with “@” or replacing “1” with “!”. These methods significantly shorten the time to crack passwords of a given complexity and length by accounting for the most common possibilities and ruling out the least common.
Today, hackers also mine public information about targeted users including readily available information such as birthdates, family member names, family member birthdates, anniversaries etc. Add to this the current practice of mining social media for users’ interests, hobbies, language, and a veritable ocean of information becomes available to tailor any attack.
If your social platform footprint is extensive and you comment on classic movies, books, TV series, perhaps it wouldn’t take a hacker as long to crack your password as listed above just by character count. If you list your favorite movie as Gone With The Wind, a password of “FranklyMyDearIDontGiveADamn” may not take the over one quintillion years to crack.
Similarly, if you list your favorite book series as The Lord of the Rings and you have a password of, “On3R1ngT0Rul3Th3m@ll”, it may not take the over one quintillion years to crack but it still may take longer than 90 days. Or maybe not. “The Prophecy of the North” on the other hand may suffice if you can reliably type it each time but that’s an example of a password (or passphrase) that’s so complex that it actually may be detrimental to actually use it in practice.
So, when making passwords keep in mind that:
- If you’re changing your password every 90 days, you need a password that can’t be cracked in fewer than 91 days
- Don’t use personal information that can be gathered about you when creating a password even if it meets the complexity and length requirements
- If this seems overwhelming, consider using a password manager to generate and store sufficiently complex passwords and passphrases for you
![]() - A shy Kelser employee who wants to help you be more cybersecure
- A shy Kelser employee who wants to help you be more cybersecure
But Wait, There’s More
Hopefully you’ve had a safe Cybersecurity Awareness Month and learned new ways that you can help protect your personal data and your organization’s data from cyber criminals.
If you’d like even more ways to improve the cybersecurity at your organization, jump over to the Kelser Learning Center or download the free 10 Simple Things You Can Do to Improve Your Company’s Cybersecurity Posture eBook.
Stay safe out there and here’s hoping for a cyber-safer tomorrow.