NIST 800-171 vs CMMC:What’s The Difference? How Do They Work Together?
If you are a company that works with the government you are familiar with the rules and regulations that surround information labelled as sensitive, top secret or classified. You most likely know about the National Institute of Standards and Technology (NIST) Special Publication 800-171 and Cybersecurity Maturity Model Certification (CMMC).
They both are important, but what’s the difference, how do they work together and what do they mean for your organization?
The goal of this article is to answer those questions and help you understand why it’s important to be compliant if you are a contractor, subcontractor, or supplier for the U.S. government.
We work with companies of all sizes, including contractors, subcontractors, and suppliers working for the U.S. government. We’ve helped organizations just like yours through NIST 800-171 compliance, so we know what’s involved.
After reading through this article, you’ll have a better understanding of these crucial cybersecurity frameworks, know the differences and how they work together.
You will also be able to make an informed decision on the benefits of following the NIST SP 800-171 cybersecurity framework, what it means for your business, and what actionable steps you need to get started for compliance.
What Is NIST 800-171?
In 2003, FISMA (the Federal Information Security Management Act) was enacted. Shortly after, the National Institute of Standards and Technology (NIST) created Special Publication 800-171 to provide a framework for protecting CUI.
What Is CUI?
CUI is unclassified information that is created or possessed by the U.S. Government or an entity on behalf of the Government that, being relevant to the interests of the United States, requires safeguarding from unauthorized disclosure.
What Is CMMC?
The Department of Defense (DoD) first introduced the Cybersecurity Maturity Model Certification (known as CMMC) in 2019. CMMC 1.0 followed in early 2020, but small and medium-sized businesses quickly objected to the complexity of the framework and assessment process outlined in CMMC 1.0.
As a result, the CMMC guidelines were refined, and CMMC 2.0 was born. The CMMC 2.0 Final Rule went into effect on December 16, 2024.
The goal of CMMC is to protect sensitive federal information shared within the U.S. Defense Industrial Base (DIB) supply chain and the contract information necessary to produce the parts, systems, and components necessary for national defense.
Related Article: How To Find CUI Within Your Environment & Set A CUI Boundary For CMMC
The regulation does this by validating the safeguards and practices put in place to ensure basic cyber hygiene and the protection of federal contract information (FCI) and controlled unclassified information (CUI) within the supplier and partner networks of the DIB.
What Are The Differences?
Now that you know what NIST 800-171 and CMMC are, here is a table highlighting the differences.
|
NIST 800-171 |
CMMC (v2.0) |
|
|
Type |
Framework |
Certification Program |
|
Implemented By |
National Institute of Standards and Technology (NIST) |
Department of Defense (DoD) |
|
Applicability |
Voluntary |
Mandatory for DoD contractors handling CUI Based On NIST 800-171 Controls |
|
Focus |
Security controls for CUI |
Cybersecurity Maturity Levels Assessment, re-attestation requirements enforced by DoD |
How Do NIST 800-171 & CMMC Work Together?
You can think of CMMC as a certification program while NIST is a framework that provides a set of guidelines and essential security controls. CMMC does not specify its own security controls from scratch. Instead, it leverages the controls outlined in NIST SP 800-171 and builds on them by introducing additional security controls and maturity levels.
This means that if your business is NIST 800-171 compliant, you already have a good head start toward CMMC certification.
Related Article: What Is CMMC Compliance? 5 Key Steps To Help With CMMC Certification
Why CMMC Compliance Matters For Your Business?
If you are a company that works with the DoD or handles FCI or CUI, understanding and becoming compliant with NIST 800-171 and CMMC is crucial. Here’s why:
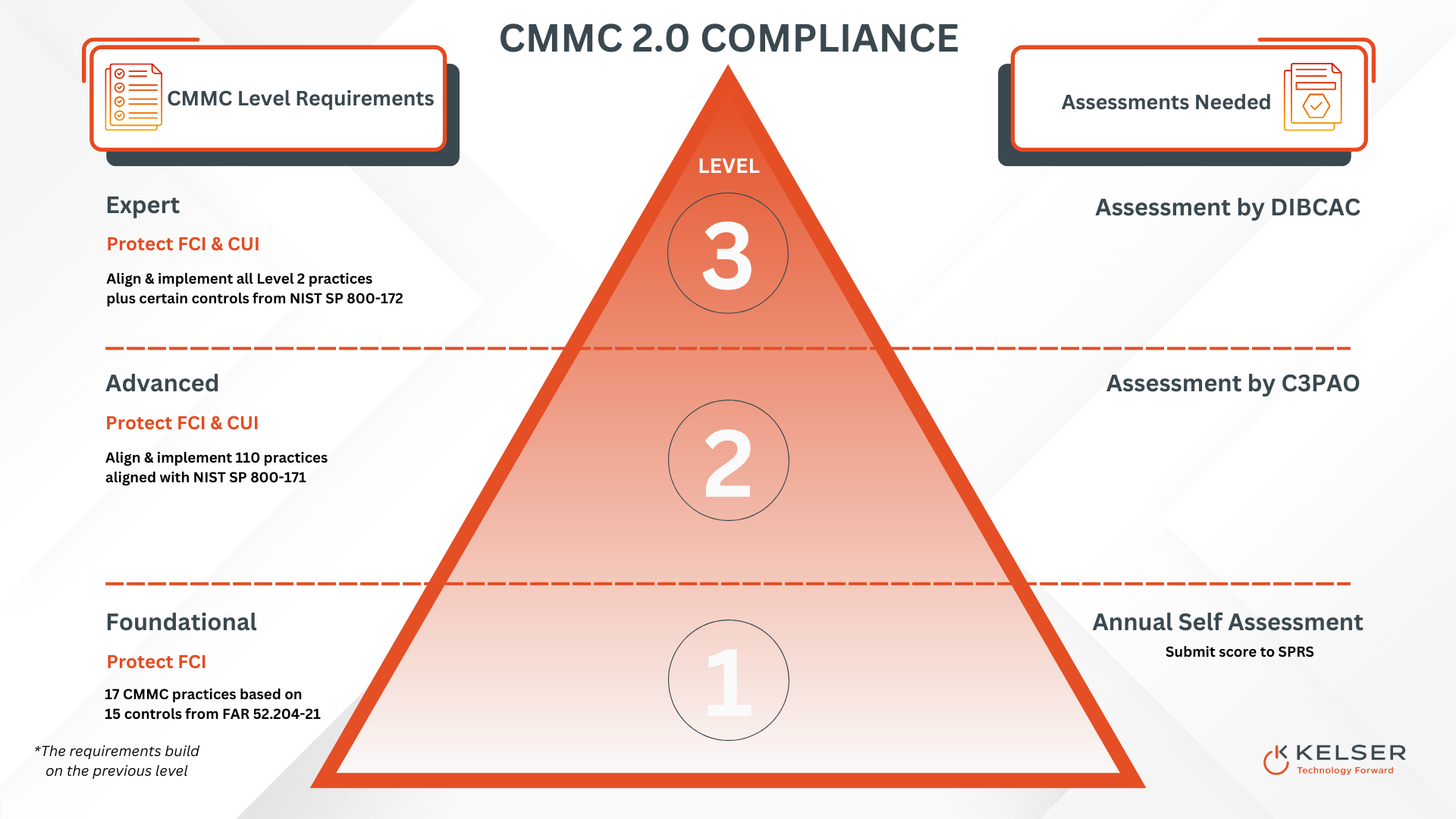
CMMC compliance is now mandatory for defense contractors and sub-contractors who work with the DoD. CMMC requires either self, third-party, or federal assessments to determine their level of compliance with the requirements outlined in CMMC 2.0.
Your organization’s ability to meet foundational (Level 1), advanced (Level 2), or expert (Level 3) standards associated with CMMC 2.0 will determine your eligibility to maintain your existing federal contracts and compete for others.
A failed CMMC assessment could potentially lead to lost contracts, loss of revenue, and even business closure.
While even if CMMC doesn’t directly affect your organization, by following the best practices and security controls outlined in NIST 800-171 you can put your company in the best position to work with the DoD in the future, because you are demonstrating your commitment to good cybersecurity hygiene and protecting the valuable data of your clients.
Related Article: How Zero Trust Can Streamline NIST & CMMC Compliance For Your Business
What Steps Can I Take For Compliance?
1. Understand NIST 800-171 & CMMC
Make sure your organization thoroughly understands the CMMC regulatory requirements and NIST SP 800-171 controls it’s based on.
You'll need to determine your CMMC level in order to know the security controls and assessment requirements you'll need to satisfy.
2. Conduct A Self-Assessment
Conduct a self-assessment and identify areas where your cybersecurity protocols maybe lacking and develop a plan to address these gaps. Use the controls outlined in the NIST 800-171 framework as a guide to evaluate your current cybersecurity posture.
You can submit your self-assessment into the DoD's Supplier Performance Risk System (SPRS) to get a baseline of your current cybersecurity maturity.
Be aware that part of your self-assessment will be figuring out what type of CUI you handle and where it lives within your environment.
Once this is done, you can set a CUI boundary to narrow your compliance focus to only in-scope areas.
This will save you significant time and money in implementing the right security controls to protect the sensitive federal information you handle within the pre-determined scope.
3. Identify And Address Gaps
Once you've identified the security gaps within your scoped environment, you'll then need to create a defect implementation plan. This plan will outline the exact security measures you intend to put in place to fix those cybersecurity vulnerabilities.
This may involve implementing new security controls and updating policies and procedures.
Related Article: CMMC Step 2: How A Gap Analysis Can Help You Find Your Security Risks
4. Develop A System Security Plan (SSP)
A System Security Plan (SSP) is an essential requirement for both NIST 800-171 and CMMC. This document spells out the specific policies, procedures, and controls your business has implemented to safeguard FCI and CUI.
The comprehensive document will spell out your organization's cybersecurity strategy.
It will serve as your evidence to the certified third-party assessor organization (C3PAO) you hire for your assessment to prove that you've adopted the necessary security measures to protect the federal information you handle to meet CMMC compliance.
Your SSP must include your access control measures and your incident response plan as part of your documentation. Keep in mind that all documents included in your SSP must be finalized to be accepted.
Related Article: CMMC Step 4: SSP Documentation–What’s Your CMMC Compliance Evidence?
The Bottom Line With CMMC Compliance
After reading this article, you now have a thorough understanding of what NIST 800-171 and CMMC are, how they differ, and what becoming compliant means for your business. You've also learned actionable steps to start your journey to achieve compliance.
Your organization may or may not need help implementing these steps. Only you can decide if you have the internal resources you need to carry out such a complex undertaking.
Our experience has shown that companies that are successful at implementing the steps required for NIST 800-171 and CMMC compliance using internal staff typically have the following characteristics:
- a large enough internal IT team that several of them can pull away for an extended period to hyper-focus on implementing the necessary controls without negatively impacting your other internal IT support needs
- certified CMMC experts on staff who have prior cybersecurity compliance experience
If your company doesn’t fit the above criteria, working with a managed IT services provider (MSP) may offer advantages by avoiding common mistakes that could compound the time and cost involved in reaching compliance.
Managed IT support solutions help organizations like yours adopt many of the requirements outlined in NIST 800-171 and prepare for CMMC certification.
You'll also get customized support, offering strategic guidance and recommendations for security solutions tailored to your business.
We know managed IT services isn’t right for every organization. We publish articles like this one so that business leaders like you have the information you need to keep your data and infrastructure safe, whether you choose to work with us or not.
Use the button below to start a conversation with us about any questions you may have on CMMC certification and see how we can help you navigate your compliance journey.





