Business IT Assets: Lifecycle Stages & Optimal Refresh Cycles
IT hardware, like a vehicle, begins to lose value the moment you purchase it.
Technology is an ever-evolving landscape and what’s new today, will soon be replaced by newer devices and software with enhanced performance and safety features. With this in mind, how often should you refresh your IT assets?
At Kelser, we’ve been helping answer this question for customers every day for more than 40 years.
In this article, I’ll walk you through the factors to consider, so that you can maximize the value of your purchasing dollar while keeping your IT infrastructure operating effectively to meet the needs of your users and customers.
We’ll explore what IT assets are, the five IT lifecycle stages, the replacement timeline, and why planning ahead is key to cost-saving.
After reading this article, you’ll know how to stay ahead of the curve when it comes to providing long-term care and planning for your IT assets.
What Is An IT Asset?
I always find it’s best to start at the beginning.
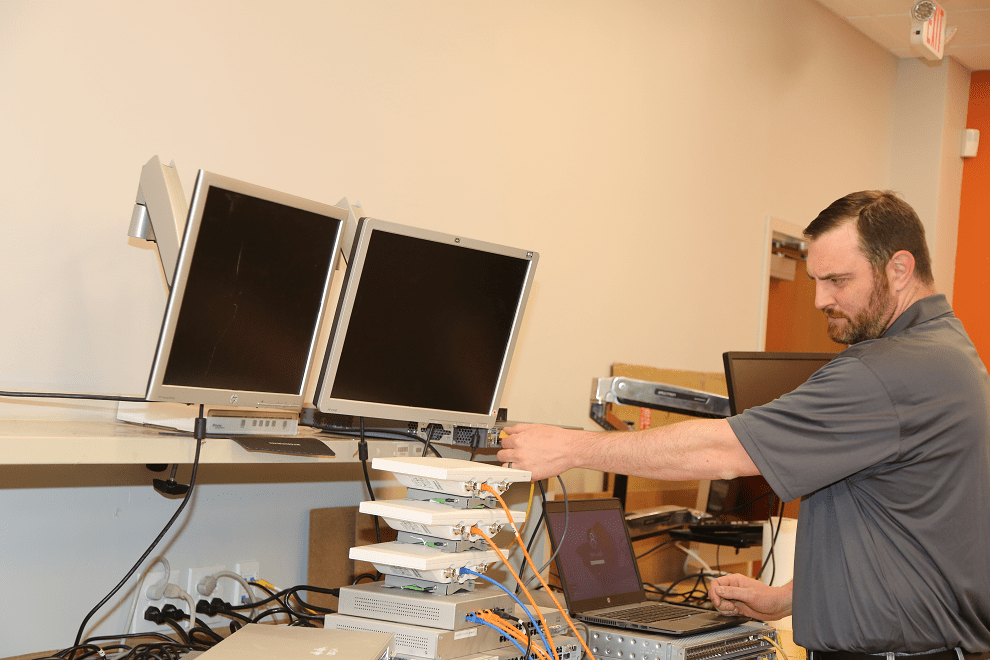
For anyone who may be wondering, the term IT asset refers to any piece of hardware or software that is used by your business. Servers, network devices, printers, switches, devices (laptops, tablets, desktops), and the associated hardware that keeps them running are all IT assets.
What Are The 5 IT Asset Lifecycle Stages?
There are five stages in the lifecycle of any IT asset (server, device, network, etc.).
1. Procurement
The first stage is product purchase.
Bulk-buying programs may be an option. Other key considerations are the capability of the equipment, the warranty and service package, scalability, and any accessories you may need for your particular installation.
2. Deployment
The second stage happens when the product is configured for your organization and readied for use.
This can include delivery, set up, imaging, installation on the network, and creating user profiles.
Make sure to note the location of the asset, so that you can track which devices are located in which physical location. This will make ongoing management and eventual asset disposition easier.
3. Use, Monitoring & Management
The third phase begins when the product begins active duty for your organization. This phase also includes monitoring, updating, patching, and overall maintenance and upkeep.
Related article: Why Do I Need To Patch And Update Business Software & Operating Systems?
You can’t protect against threats you don’t see, that’s why active monitoring is important. You need to know which devices are accessing your network so you can make sure there are no unauthorized users who might be looking to do harm.
In addition, processing speeds can indicate something is amiss, so keeping tabs on them can detect untoward activity, too.
It’s important to have a regular schedule for installing developer updates and patches that are issues to improve performance and plug security gaps.
Malware scans, safety protocols, and patch upgrades will help keep machines operating optimally and will prevent premature deterioration.
Related article: The Differences Between Vulnerability Scans & Penetration Tests
4. Upgrade
No matter how well you care for your devices and software, they will eventually outlive their usefulness and will need to be replaced. But, before that happens you can often extend the life of your IT assets with hardware upgrades.
Maybe you can install more recent versions of software or add memory. These small changes can be an effective way to enhance performance, improve security, maximize your investment, and give you time to get your new devices in place.
Keeping track of the IT assets you have and knowing their physical location will help you track which items are coming to end-of-life and explore opportunities for upgrading hardware rather than replacing it.
Related Article: Why Businesses Must Budget For Security (& How Much)
5. Refresh
Even the best cared for infrastructure and devices will need to be retired eventually. Technology improvements happen fast and bring opportunities for performance and safety enhancements that are worthy of investment.
Organizations that plan ahead for refresh cycles are ready both in terms of financial and support resources. Part of that planning process needs to be safely taking the device out of service, removing sensitive data, recycling, and replacing it long before it actually breaks down.
How Often Do I Need To Replace IT Assets?
In general, most providers recommend replacing IT assets every three to five years. Don’t panic, though. You don’t need to replace everything at once!
Your IT organization (or an external provider if you don’t have an internal staff), can assess your network, users, workload, and tools to recommend an optimal refresh cycle for you. The refresh plan can be implemented in phases, so that the refresh is rolled out in a series of budget-friendly stages.
Proper planning and budgeting can make this a straightforward process and minimize surprises. And planning ahead often yields cost advantages due to bulk purchase discounts.
What Can Happen When Organizations Don’t Plan For Refresh Cycles?
As with most things in life, waiting until the last minute to replace your hardware isn’t ideal for a number of reasons:
1. Downtime
When machines fail, it can often result in significant worker and network downtime.
2. Wasted Resources
Waiting until the machine malfunctions can waste IT resources, since IT support workers will typically become inundated with support calls as your devices age and reach end of life. In addition, when warranties expire that makes supporting those devices more difficult.
3. Inefficiency
Your workers’ efficiency will be slowed due to the machine’s disintegration and frustration levels will increase.
4. Increased cost
You won’t be able to plan ahead for hardware refreshes financially, and will therefore be unable to leverage bulk-purchasing agreements.
What’s The Bottom Line?
After reading this article, you have a complete understanding of the lifecycle of IT devices and software. You understand the five phases: procurement; deployment; use, monitoring & management; upgrade; and refresh).
You know that most IT experts recommend replacing IT assets every three to five years and that upgrades can ensure that you get the maximum performance before replacing your devices.
As we’ve discussed, proper planning can save you valuable staffing and financial resources, while minimizing the time, hassle, and expense of caring for machines that are past their prime.
Just as you save money keeping a vehicle past its prime, there comes a point where the repair costs and hassles begin to outweigh the value.
Now that you know the downsides of keeping your IT assets past their prime, work with your internal IT organization to develop a list of your current assets, a timeline for upgrades, and replacements and approach things in an orderly fashion.
This will give you the confidence you need to ensure that your business is operating optimally and safely at all times.
If you don’t have an internal IT staff or they are stretched thin dealing with the everyday demands of supporting your users, you may be considering hiring an external provider to handle this important strategic planning process.
I have one word of advice: compare several providers to ensure you get one that is the right fit for you.
Not sure where to begin? Learn the 10 best questions to ask any IT provider. This list of questions is based on our 40+ years of providing IT support for organizations of all sizes.
Or, maybe you are wondering if there is more to hiring an IT support partner than technical skills. Here are 10 qualities to look for in an IT provider.
One of the topics that seems to be top of mind for all business leaders is cybersecurity. If you are unsure whether your organization has all of the protections you need and prefer to conduct a self-assessment, click the button below for a free checklist you can use to:
✔️Assess your organization's cybersecurity tools and identify opportunities for improvement
✔️Learn actions you can take to keep your organization's data secure
✔️Help ensure your organization follows the latest cybersecurity best practices
Or, if you prefer to have someone guide you through the process, click the button below to set up a quick phone call with one of our IT solutions experts.